|
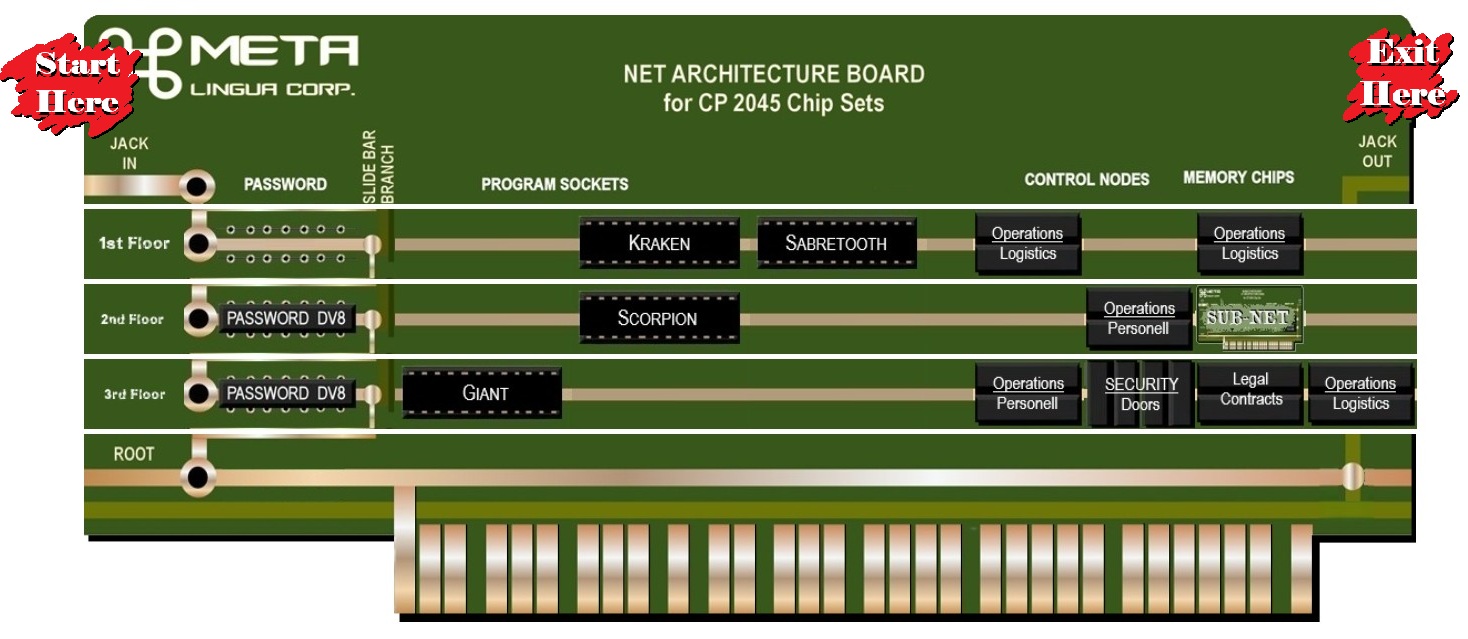
FLOOR:
Each Architecture has up to 18 levels refered to as "Floors". Floors begin at the top left side and count down resulting in the highest numbers being the lowest listed.
ROOT:
The bottom most floor is also considered the "Root Directory" or simply called, the Root. Once on the Root Floor, the netrunner can install programs that perform tasks as specified by the player and even make changes to the Net architecture itself.
|
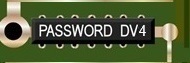 |
PASSWORD:
DV4 Reversed phone numbers, grandchildren's birth dates, and other easily guessed phrases.
DV6 More sophisticated challenges, but still easily deduced with a bit of gathered knowledge.
DV8 Often computer generated codes updated daily using an algorithm that is itself encrypted.
DV10 The highest limitation of human encryption taking both content and time of entry into account.
DV12 Cutting edge computer cryptography at the edge of cracking the secret to quantum computing.
|


|
PROGRAMS: Factory Made
Official cihps are prefered, but Details of factory chips are in the Cyberpunk Red roleplaying game rules. Second to factory made are the so called "in-house" products which are programmed by trusted technicians operating within the corporate structure.
PROGRAMS: Homemade and Pirated
Cheap and readily available at all night markets. The price does not always reflect the resulting quality. Factory chips are often outdated within a few months, but local programmers often specialize in one type of program and do their job well.
ABOUT
Unless noted otherwise, programs are restricted to their respective floor; however, like netrunners, programs have acces to any location on the floor at all times.
|
|
FILES
Represent individual reports or dosiers on various subjects. When scanned, a word-tree is generated spotlighting the most used words and phrases. Reading the document would take many minutes, but scanning takes but a second or less.:
|
 |
SUBNETS:
As they are activated for use, other Net Architectures will appear and disappear within the main architecture. Each subnet is limited in size to no more than six (6) floors.
|
 |
CONTROLERS
EIther operated by human manipulation or by demon. Controlers might be marked as "Utilites" or "Security" or other categories to ease understanding, but all are controling a physical device. |